In the vast expanse of the deep blue, where the oceans stretch far beyond the horizon, the realm of maritime communications emerges as a critical frontier. Ensuring smooth and secure exchanges between vessels and their controlling entities onshore isn’t just a luxury; it’s a necessity. This intricate dance of signals and messages weaves the framework that helps prevent collisions, facilitates trade, and bolsters the defense mechanisms of nations. Yet, lurking within the cosmos of digital data are threats lurking in the shadows, ready to disrupt this delicate balance. Welcome to the engaging dive into the world of threat analysis for maritime communications.
Unmasking the Threats at Sea
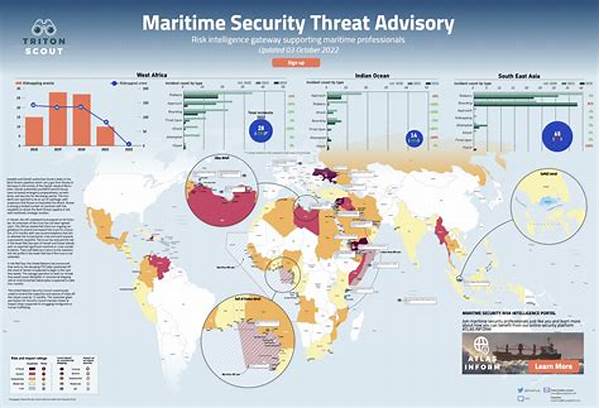
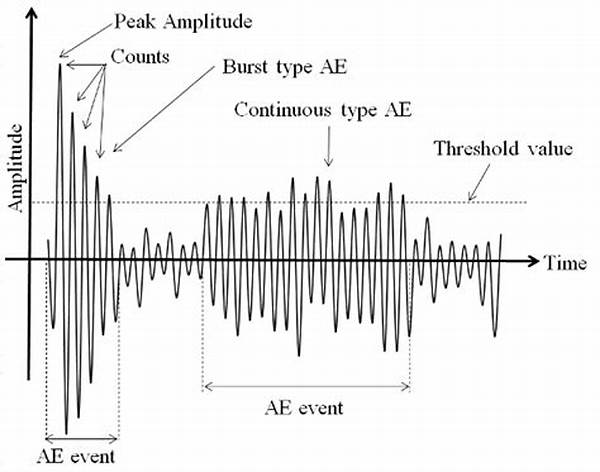
Let’s get real; the open sea ain’t just about dolphins and sunsets—it’s an arena where cyber sharks lurk. In maritime communications, threat analysis involves peeling back the layers on what could go wrong and, trust me, quite a few things can. From malicious entities attempting to intercept or alter communication, to technological quirks that leave systems vulnerable, the stakes are high. Ships rely on a flurry of signals to chat with ports and other vessels. This data-exchange party doesn’t need gatecrashers, but they’re out there, armed with everything from basic hacking tools to state-sponsored digital subterfuge. Threat analysis for maritime communications dives deep, exploring weak spots and arming ship operators with the know-how to fend off these digital bandits. So, whether its interference in GPS systems or eavesdropping on sensitive info, understanding the threats is as crucial as a sturdy anchor in a storm.
Cybersecurity: The Lifesaver
Even sailors need a lifeguard, and for ships, that’s cybersecurity. Performing a threat analysis for maritime communications feels like assembling an intricate jigsaw puzzle consisting of fancy tech gadgets, cryptic codes, and shifty hackers. Ships are like the cool kids at sea, but they need protection against bullies. Five ways to wrap your head around this?
1. Tech Shield: Think of it like a virtual Kevlar vest, stopping the bad stuff before it hits.
2. Crackerjack Coders: Making sure those code ninjas can outsmart any black hat trying to break in.
3. Stacking Firewalls: It’s like stacking blocks, but these ones keep the nasties out.
4. Signal Jammers: Keep the airwaves clear from any wannabe eavesdroppers.
5. Alert Nerds: Data detectives who catch bad vibes before they manifest.
Setting Sail with Strong Security
Yo-ho-ho, setting sail on the cyber seas ain’t what it used to be! Back in the day, all sailors worried about were storms and krakens. Now, it’s all about cybersecurity threats, baby! Think of threat analysis for maritime communications as the trusty compass telling ships where the sharks are. An effective threat analysis is like mixing a cocktail—gather the key ingredients, shake ‘em up, and hope it doesn’t spill. By scoping out vulnerabilities, maritime operators can plug holes before the ship starts leaking. Those big ol’ cargo ships? They might look like floating fortresses, but without solid threat analysis, they’re like sitting ducks in a shooting gallery. If you’re in charge, you better have these analyses handy to dodge the waves of digital danger.
Navigating Troubles and Turbulence
When the ocean throws a hissy fit, it’s the threat analysis for maritime communications that keeps everything shipshape. Those unpredictable cyber squalls aren’t just nightmares, they’re reality. Understanding how crafty hackers play their games gives operators a shot at stopping them in their tracks. Each potential threat emerges like a ghost ship, and through threat analysis, cyber sleuths figure out how to sink ‘em. It’s all about navigating those turbulent waters by beefing up defenses and devising counter-measures that’d make pirates quiver in their boots.
Battling Cyber Ghosts
Okay, let’s face it, the seas hold their spooks. Threat analysis for maritime communications is like being the ghostbuster against the phantoms cruising on digital waves. When corporate espionage wannabes go fishing (not phishing, though that’s a thing too), radar systems and data channels become their playground. That is, until some savvy threat analysis expert plays the hero and shuts ‘em down faster than a yacht outpacing a dinghy. Between fake signals meant to mislead and malware that tries to muscle in, securing maritime communications is as much about techy stuff as it is about common sense and foresight. Keep one eye on the radar and one eye on potential threats to steer clear of any nasty surprises!
Anchoring Down the Summary
Right, let’s drop anchor and take stock. The ocean is vast, beautiful, and oh-so-mysterious, but when it comes to communication, it demands sharp vigilance and robust defenses. You see, threat analysis for maritime communications isn’t just about fancy gadgets or cryptic codes; it’s the modern sailor’s mantra. By identifying risks and neutralizing them before they morph into crises, shipping companies keep their vessels afloat—in every sense of the word. Think of communication as the sea routes connecting ports, where everything from goods to data sail through smoothly. Without solid threat analysis, even the best-laid plans could run aground. Let’s salute the tech whizzes ensuring that every ship that launches returns safe and sound, digital sails intact. It’s a rough sea out there, but with proper analysis, ships can dodge the cyber-icebergs waiting in the dark depths.